
Dmytro Budorin is the co-founder and CEO of Hacken, a leading cybersecurity consulting company with an essential focus on blockchain security. Hacken offers a wide range of security services such as blockchain security consulting, web/mobile penetration testing, coordination of bug bounty programs, crypto exchange ratings, and education on cybersecurity. It was founded in August 2017 and is a part of the Hacken Group. Read and learn a real lesson about cybersecurity and vulnerabilities in Crypto smart contacts, Defi Protocols, and Exchange security levels.
Dmytro Budorin
Interview Date : 11th November 2020
- Dmytro Budorin Hacken CEO (All Interviews)
- From Government Sector to Private Sector
- Ukraine 2017 Cyber Hack Took Over the Nation
- What was the Hard part of the attack?
- Hackers Are Attacking Private People
- Young Hackers are Graduating
- Educate Yourself by Yourself
- Hacken AI
- What to Do Right Away?
- Crypto Traders Be Aware
- Why Is BTCTurk the Most Secure According to Hacken?
- One of the Most Tragic Hacks
- Is KYC User Security?
- We Need an Equilibrium
- Exchanges are Not Banks
- Crowdsource Security
- Visibility and Exposure
- Hacken Team Check
- Audit Implementations
- What is Most Vulnerable in 2020?
Dmytro Budorin Hacken CEO (All Interviews)
My name is Dmytro Budorin. I earned good karma by working for Deloitte for 8 years, but I spoiled my karma a little bit when I started to work for the government. That is when I turned to the crypto industry. I started the cybersecurity consultant company Hacken to create a safe haven for people to feel secure online. Presently, we provide multiple consultant services. We are very big crypto enthusiasts, and at the same time, cybersecurity fanatics too. We strive to make the world a safer place.

From Government Sector to Private Sector
In 2017, a virus started to spread in Ukraine, where Russian hackers attacked Ukraine. Some people are saying that it is the biggest hack attack in the world so far. At Deloitte, I became the winner of the Deloitte CIS Audit Challenge with my Audit BigData SAP solution. This solution became widely implemented in CIS offices. I ended up becoming one of the top executives within Ukraine’s military defense industry after its large-scale reform was launched by the government in 2014~2015. However, at the time of the virus attack, I was working for the Ukrainian government. It was too bureaucratic, thus I thought I and my team could be much more efficient if we worked for the private sector and gave the government services. I can say that was probably the second-best decision of my life making Hacken. My first best decision is my wife.
Ukraine 2017 Cyber Hack Took Over the Nation
Around 40% of government organization laptops were attacked by this virus. A lot of people suffered, and a lot of information was lost. The issue was that a lot of people were using one local account software that connected your basic account ledger book. That ledger was a government taxation report program that was quite easy to use. I even know the founders of this program, and they are very nice programmers. Unfortunately, the Russian hackers attacked this particular program and installed the malware inside the application update of that program. The inventors didn’t know about it. When it was time for a regular update to release some new features, the creators proposed their users to install this update, but once the customers installed it the virus got into their computers. For 2 days, the Russian hackers turned on the malware and attacked the government and citizens with it. The victims said they saw a notification message about their computer being under attack. If they did not send BTC to the mentioned address, the users’ hard drives would be inscribed to lose all data.
What was the Hard part of the attack?
The virus was not the most complicated thing. The complicated thing was how the attackers delivered the virus into people’s computers. Their approach was quite creative. The ransomware attack, called Petya, is a family of encrypting malware, and it was first discovered in 2016. Different types of Petya were first seen in 2016, which propagated via infected email attachments. However, in June 2017, the new variant of Petya was used primarily to target Ukraine and later became a global cyberattack.
It was a huge shock and eye-opening lesson for a lot of people. Government organizations were not prepared at all for this, and people are not good at informing themselves about proper virus prevention settings. Consequently, a lot of people lost a lot of data. I have been hacked once in my life, and I have broken a bone once in my life. If one of those would happen again, I would prefer to have another bone broken, but I don’t want to be hacked again. It was a painful experience.
Hackers Are Attacking Private People
Hackers are turning their attention from institutional targets to end-users and private people because it is easier and more portable. Also, hackers are lazy. They don’t want to hack a bank, because that would be like a real tough job. However, hacking people and then intimidating and blackmailing them is easier. There are a lot of people who give in. More people from developing countries are more prone to do as hackers say.
Young Hackers are Graduating
Hacking has become a trend online. There are a lot of forums and platforms, especially a very big Russian forum where you can do a course on how to hack an individual. Thus, a lot of 14~15-year-old children do those courses, and after a couple of months, they start hacking and attacking people online. Unfortunately, it is reality. Today, you can find anything on the internet. In the Russian language, such online sites and such promotions are not banned. There are ways to ban such websites, but no one is doing anything about it. Then authorities do not consider such issues, similar incidents will happen in all countries around the world.
Educate Yourself by Yourself
What you can do as a user is keep educating yourself. Cybersecurity is not that difficult of a thing if you just follow some simple rules. The rules include always using different passwords for different accounts, and always using a 2-factor authentication application. It is better to use a password manager application. Also, you should not link your password and 2-factor authentication to a sim card, especially not if you travel a lot. Next, you should always subscribe to a darknet counter tool to be alerted if your data is leaked from somewhere. If you follow these basic rules, hackers will need more time and effort to hack you. So, they will just say “no thank you” and find another person to hack. Approximately 70% of the people who use the same password all the time are most likely to get hacked.
Hacken AI
Hacken was created by 2 cybersecurity companies emerging in 2017. We combined our forces to become a strong player in the blockchain security market. The main thing we do is to educate people, and we try to educate people from different aspects. For example, we have a project called the Crypto Exchange Cybersecurity Ranking service where we are constantly monitoring exchanges’ security. We provide users with information about what exchange does to improve their cybersecurity. We think that’s very important to be aware of because a lot of exchanges do not pay enough attention to this aspect although they may say “we are the most secure” or “ security is our highest priority”.
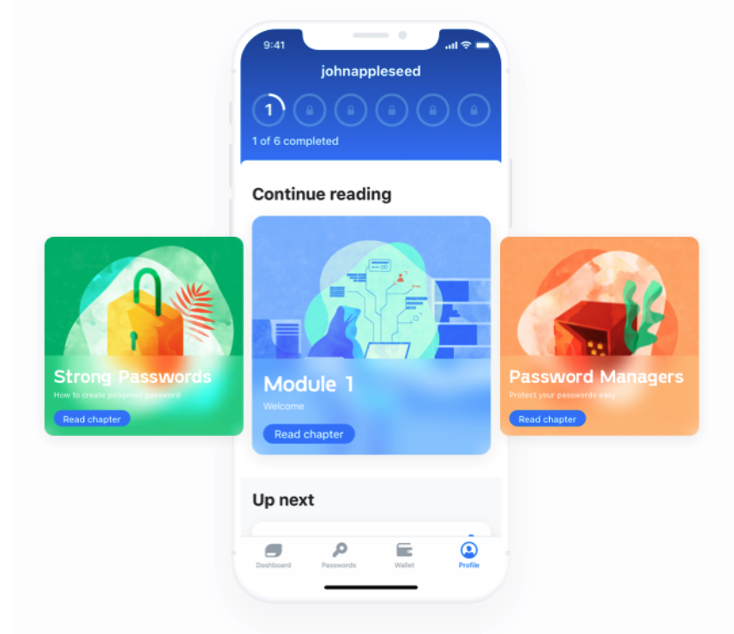
The second thing that we are building is an application called Hacken AI. This application is for the user to reach individual cybersecurity perfection.It is a unique educational program on the main cybersecurity topics including Account Management, Anti-Phishing, Privacy, and many more. Users can learn how to stay secure, and get to know essential basics about cybersecurity. It is to be released in 2021.
What to Do Right Away?
The most important thing is to know how you can back-up your passwords and security level. People are lazy sometimes, and they don’t take some proper steps to make sure that “if you need the back-up information, you will find out where it is”. People do screenshots of passwords or important information, but what happens when they lose their phones? They will have no methods to take back their wallets.
When you buy jewelry or something very expensive, you make sure to protect it. You don’t just put it on a bookshelf, but you keep it in a safe. It usually will be a place you trust. You have to start thinking the same about your passwords you need to safely back it up. A screenshot is not enough. Hacken AI, for example, includes Account Management, Anti-Phishing, Privacy, etc., and with such password and information managers, you can keep your information safe.
Crypto Traders Be Aware
If you are a user, a holder, or do crypto trading, spending 10 minutes and creating a proper plan to back up all your passwords is smart. If you have 4~5 wallets, and your passwords are all over the place on an excel sheet or in a word document on your laptop, it is not safe. It is very risky. You should either put it down on paper, and put it in a very safe place, or in a password management app or tool by trusted makers.
Some people keep their passwords in apps like Evernote. For those people, I want to remind them of the case of Ian Balina, a famous YouTuber who also backed his passwords and information in Evernote. He was hacked online when he was doing a Livestream YouTube video in 2017. Due to that hack, he received damage of more than 2 million dollars’ worth of tokens. The incident was devastating, but the case was quite simple. The backup information for his wallet had been stored in his Evernote. Also, his computer was connected to the internet. The hacker found Ian Balina’s email address on the internet and went to the dark web to find the password of Ian Balina. That was a password Ian Balina had used in his college days, but the hacker still inserted the email address and the password to Ian Balina’s Evernote. Unluckily, the hacker was able to log in as it was still the same password for the Evernote. Then, he got the password, etc. back up to Ian Balina’s wallets, and stole all his assets worth 2 million dollars. This should be a lesson for all of us: don’t keep your backups and passwords in any online tools.
Why Is BTCTurk the Most Secure According to Hacken?
There are different types of people who create and establish exchanges. In most of the cases, unfortunately, the founders of some PR business developers and marketing business people who know how to promote and sell, but don’t know about the technology behind it. In very rare cases, actual IT and CTO are founding and managing exchanges. An example of that is CZ’s Binance; it is quite secure in its security level.
BTCTurk is another rare case where IT people have created the exchange. They are perfectionists in testing their exchange’s cybersecurity and maintenance. Most exchanges do the exchange cybersecurity level test after the launch, but they did it before the launch. Also, it is the biggest exchange in the Middle East region.
Just like in Russia, and anywhere else in the world, there are hackers from all places in the world who try to hack exchanges every day. Certainly, hackers will try to hack BTCTurk as well. Hence because of that danger, they have to take several measures to protect their exchange. I don’t think that it is an unexpected result that BTCTurk is the most secure exchange there is because it is a result of hard work from great IT people.
Turkey has many Bitcoin fanatics, and daily around 3000 BTC is transacted in that area. It is estimated that Turkish users have Bitcoins of approximately 30 billion dollars, and this number is on the rise.
One of the Most Tragic Hacks
Back in 2017, people were keeping their assets on a hardware wallet. There was one individual who faced a massive hack and lost around 60 million dollars’ worth of assets on his hardware wallet. The attacker knew that this guy was using that kind of wallet, and targeted his attack by delivering a fake software update for the wallet. The holder didn’t see that the message wasn’t from the official wallet administrators and when he opened the software it didn’t go to the official homepage for the update either. Still, he didn’t think much of it and clicked “yes” to the update. Seconds after, the fake uploader started to install the fake wallet and stole everything on the wallet. The poor guy lost 60 million in a few minutes by just installing the wrong software update. So, what I am trying to say is that you should never install anything that is not from licensed stores.
Is KYC User Security?
KYC is usually needed for other purposes than for user security. I don’t think KYC has to do with individual security. For example, if a hacker hacks my account and steals all my BTC from my account, the KYC will not protect or help me in regaining my BTC back. I still will lose my BTC, and no one will help me. So, it is mostly for exchanges to confirm people’s identities so they do not register fraud, a money launderer, or drug trafficker, and hackers into their exchange. It can help in finding criminals if the exchanges create a good relationship with the police, for example. However, we haven’t seen much of such cooperation yet. Many people in the space are saying that blockchain should be decentralized and that we don’t need KYC. They state they need freedom and do not want any restriction on it.
We Need an Equilibrium
We need to decide what we want: do we want mass adoption, or do we want this technology to be used by thousands of people with no structure? It is obvious to me that mass adoption will come only if this technology is safe to use. Thus, without all these measures and some regulation by authorities, it is not safe to use. I think governments like the Japanese government are doing a good job of being cautious, and they are putting very strict requirements for cryptocurrency exchanges. The Japanese government goes to the extent where they are reviewing the balances of each exchange. They confirm how much money is on the balance of an Exchange, and how much money was deposited by the customers. Those have to match, which is what the Japanese government is checking.
On the contrary, an exchange that is registered on some island that no government or authority cares about, no one knows what is behind the exchange, or who is even behind the exchange. These kinds of exchanges receive people’s deposits and spend them. So, when the users of those exchanges demand their money back, the exchanges do not have the money to give back to the users. We will see much more of such failures in the future if we don’t create an equilibrium between regulation and the crypto industry.
Exchanges are Not Banks
People don’t understand the risks with crypto, and why regulators and exchanges have to take strict and drastic measures. Many think that a crypto exchange is the same as a bank, so if you put money in it, they will certainly get their money back. Different from exchanges, banks are very regulated and have a lot of measures in place. However, if a cryptocurrency exchange collapses or is hacked, all the accounts will be closed with all the money gone. When that happens, you cannot go to the government and ask for help. The government will say “sorry, but it is unregulated”, and so they cannot take any action. Hence, governments must regulate to a certain degree for mass adoption. I am a very big fan of mass adoption, but every exchange that is not regulated will 95% of the time exit and scam people one day. It is just a matter of time.
Crowdsource Security
Crowdsource security is an organized security approach where several ethical hackers are hired to search for and report vulnerabilities on an exchange, and this is called bug bounty programs. Such measures may be conducted by an exchange, and by professional platforms. Unfortunately, some exchanges don’t have any bug bounty programs at all, meaning the exchange doesn’t know about their security vulnerabilities. That is why we underline the importance of bug bounty programs to all the exchanges.
Visibility and Exposure
Historical cases are about whether the exchange has been hacked or not in the past. An exchange that has never been hacked before gets a score of 10. Anything below that means the exchange may have been attacked or hacked before. Every exchange is under constant attack every day, so one has to be careful. Despite that, a lot of exchanges are trying to get listed on CoinMarketCap or CoinGecko. Although CoinMarketCap and CoinGecko have pretty strict requirements, once an exchange is listed, an army of hackers will start to attack your exchange. With an insecure level of security, and for example no bug bounty programs, the hackers will just vanish all money from the exchange. Hackers are monitoring every new exchange on CoinMarketCap, CoinGecko, and similar sites. Once they are listed, the hackers try to hack them as the newer ones are an easier target.
Hacken Team Check
We register an account, deposit money and funds in it on all known exchanges. Through this process, we can go through the security check level of those exchanges, and later give them a report of the exchange security level. We look at how the exchange functions, and so behind our reports, there are a thousand hours of work.
We are also thinking about creating a ranking of mobile wallets for NFTs. NFTs are becoming very popular right now, so we want to register a research site to help people and navigate them towards wallets that are safe to use.
Server Security
Server security is about how the exchanges are protecting the exchange central infrastructure. If an intruder finds vulnerabilities in certificate measures in the server system, all the server components will be compromised. This may lead to massive monetary damage. With our Server Security measures, we examine the server security of exchanges.
User Security
User security is interesting because when you are creating an exchange, you have to create a puzzle. In that puzzle, you can make it easy for people so they can create an account with only 4 to 5 clicks to join. Or you can make it hard by creating different layers of confirmations for security. With the latter, you will not be able to open an account with only 4 to 5 clicks. It will take longer to open an account and start trading. Some exchanges select the first option for easy onboarding. Unfortunately, sometimes they can be very greedy, and do not install the necessary measures to protect users from setting up wall security characteristics like strict password requirement, Captcha, or 2 Factor Authentication.
Captcha
Captcha is important because it provides protection from brute force. Brute force is a technique where a hacker can try to log in with different passwords infinitely for the same email address. If an exchange does not set up a captcha, it makes them vulnerable to brute force hacking techniques. And yet, as you can see from the graph, around half of the exchanges have not set up Captcha.
Missing Headers
Missing headers means the data you are inserting into the exchange is not properly encrypted. Thus, the data can be intercepted by an attacker when you do a transfer at any given time. Let us say, you are transferring data, and at that time an attacker is intercepting that transfer. The hacker can change your password, and you will not be able to log in to your account again after that.
Audit Implementations
We usually perform Smart Contract Audits and Defi Audits. During such investigations, we imitate an attacker’s behavior and try to detect vulnerabilities with the smart contract or DeFi project protocol. This involved us developers scrutinizing the code that is used to underwrite the terms of the smart contract or the protocol. We make a report out of the results, and this allows the company to identify any potential bugs or vulnerabilities before it is deployed.
What is Most Vulnerable in 2020?
I think Defi is the most vulnerable right now because there are a lot of PR and Marketing guys who have gotten into it. Many don’t know the technology and think they can copy and paste a code from a token swap, and just make some money, but it is not that easy. Therefore, users have to take a proper review of who is behind it before investing in a DeFi project. If it’s not clear, then it is not a good idea to invest in it, and it has become too easy to lose money in Defi.
Interviewer , Editor : Lina Kamada
【Disclaimer】
The Article published on this our Homepage are only for the purpose of providing information. This is not intended as a solicitation for cryptocurrency trading. Also, this article is the author’s personal opinions, and this does not represent opinion for the Company BTCBOX co.,Ltd.

